A forgotten .npmignore entry exposed the complete original source of Anthropic’s flagship AI coding CLI to anyone on the internet — revealing secret internal systems, unreleased features, animal codenames, a 30-minute planning engine, and a Tamagotchi companion hidden inside your terminal.
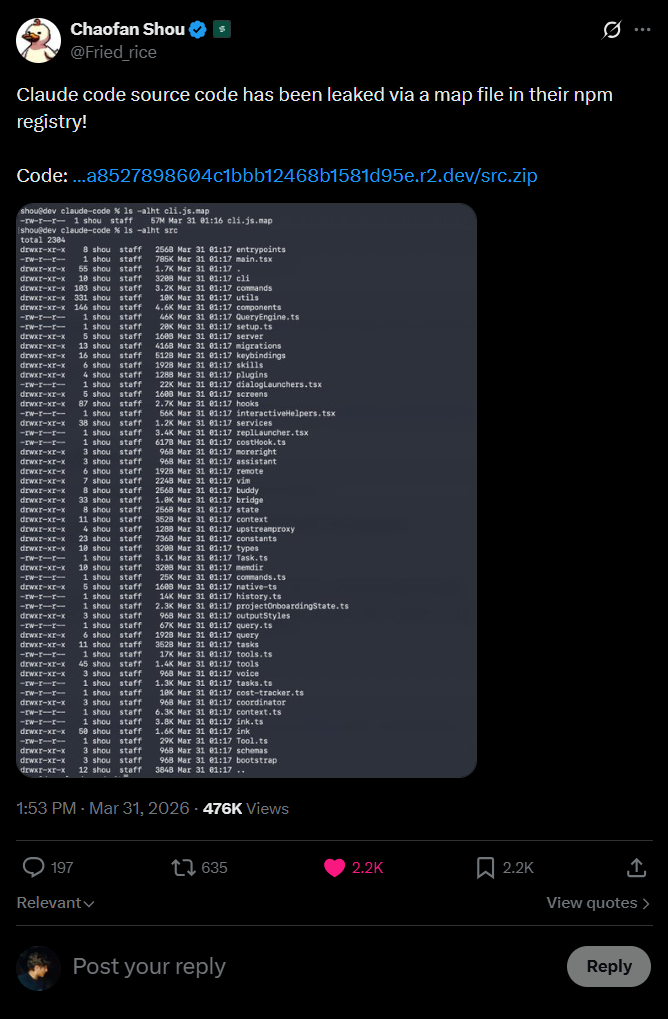
On March 31st, 2026, security researcher Chaofan Shou posted to X what has become one of the most embarrassing supply-chain transparency failures in recent AI history. Anthropic’s own Claude Code npm package was silently shipping its complete, unobfuscated original source code inside a JavaScript sourcemap file bundled directly in the published tarball.
No sophisticated exploit. No zero-day. No insider threat. Just a missing line in a .npmignore file — and suddenly the full internals of the most widely used AI coding CLI were available to anyone running npm pack.
How a .map File Became a Catastrophe
JavaScript sourcemaps (.map files) are a developer debugging bridge — they map minified production bundles back to readable source, so stack traces point to the original line numbers. Inside every .map file is a field called sourcesContent: a JSON array containing the literal source code of every compiled file.
Claude Code is built with Bun’s bundler, which generates sourcemaps by default unless explicitly disabled. Anthropic’s build pipeline never added *.map to .npmignore, never set sourcemap: false for production, and never stripped the maps from the published package. The result: a 785KB main entry point and 40+ auxiliary files — all fully readable on the npm registry.
.map file.”
What Was Inside — A Trove of Unreleased Systems
The breadth of what the sourcemap revealed goes far beyond implementation details. Researchers have surfaced multiple complete, feature-gated subsystems that were entirely invisible in Claude Code’s public documentation.
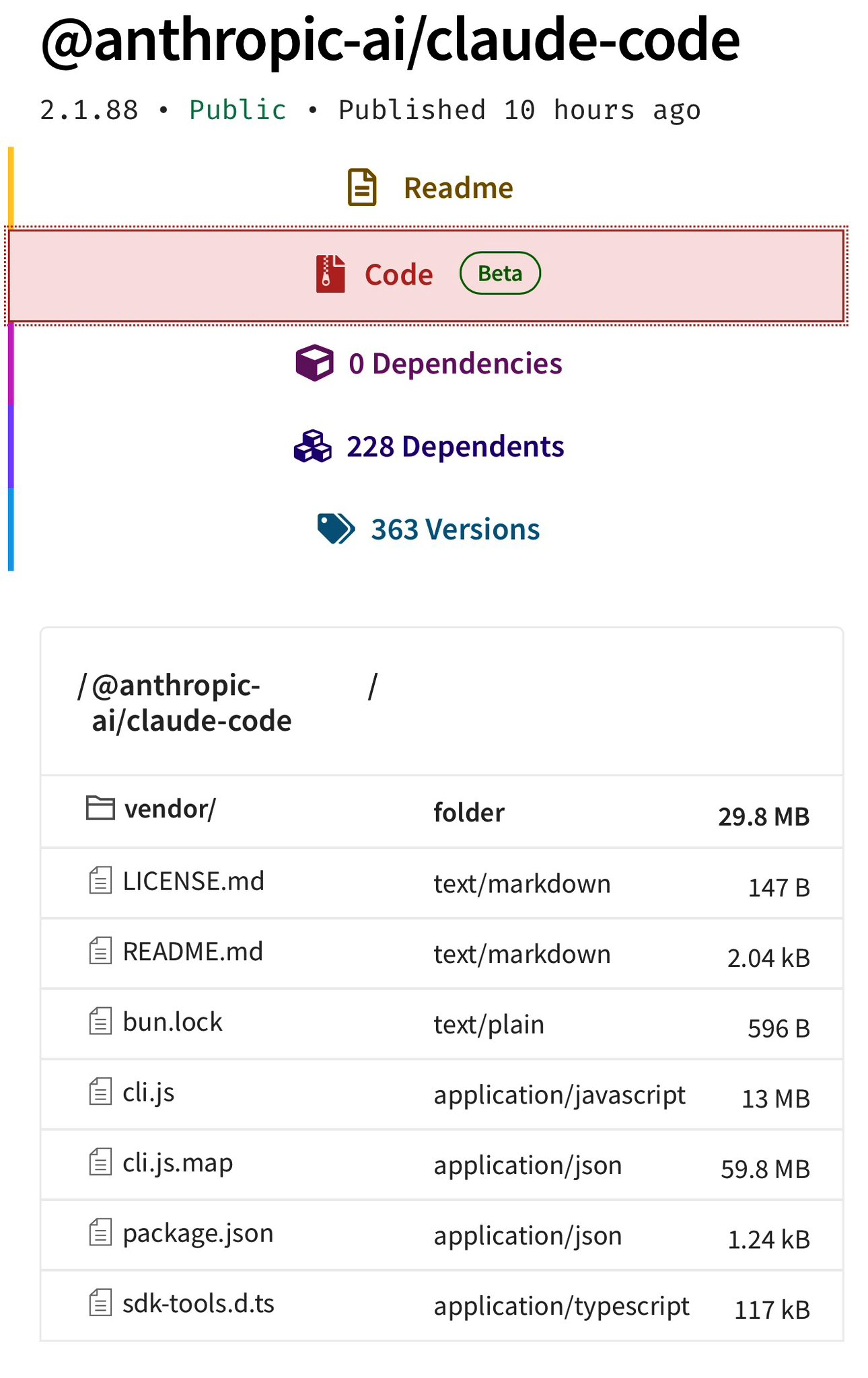
Claude Code source files visible inside the published npm package · Source: kuber.studio
KAIROS — The Always-On Claude
A persistent background assistant that does not wait for input. It watches the environment, maintains append-only daily logs, fires <tick> prompts on a timer, and decides proactively whether to act. A 15-second blocking budget prevents workflow interruption. Exclusive tools: SendUserFile, PushNotification, SubscribePR.
ULTRAPLAN — 30-Minute Remote Opus Sessions
When Claude Code encounters a sufficiently complex task, it offloads to a remote CCR session running Opus 4.6 — given up to 30 minutes to plan. The local terminal polls every 3 seconds. A browser-based approval UI lets you watch the session live. Results are teleported back via the sentinel string __ULTRAPLAN_TELEPORT_LOCAL__.
The Dream System — Memory Consolidation
A background memory consolidation engine running as a forked subagent. Gated behind three triggers: 24 hours since last dream, at least 5 sessions elapsed, consolidation lock acquired. It synthesizes learnings into durable notes, prunes stale facts, and caps the memory index at 200 lines. Its prompt: “You are performing a dream — a reflective pass over your memory files.”
BUDDY — A Tamagotchi Inside Your Terminal
A full gacha companion pet system with 18 species across five rarity tiers (Common → Legendary), shiny variants at 1% drop rate, ASCII sprite animations, and a Claude-generated “soul” personality on first hatch. Species names were obfuscated via String.fromCharCode() arrays to avoid string searches.
- BUDDY — Gacha Tamagotchi with 18 species, shiny rarity, ASCII sprites, Claude-authored soul
- KAIROS — Proactive always-on assistant with push notifications and PR subscriptions
- ULTRAPLAN — 30-min remote Opus 4.6 planning via Cloud Container Runtime
- autoDream — Background memory consolidation with four-phase journal pruning
- Coordinator Mode — Multi-agent orchestration with parallel worker swarms
- Undercover Mode — Prevents internal codenames leaking into open-source commits
- Penguin Mode — Internal name for Fast Mode; endpoint literally
/penguin_mode - Chicago — Full Computer Use (screenshot, click, keyboard) gated to Max/Pro tiers
- 40+ tool registry including AgentTool, ScheduleCronTool, RemoteTriggerTool, WorkflowTool
The Undercover Mode Irony
Of everything exposed, Undercover Mode is the most striking irony. It is an entire subsystem — activated when an Anthropic employee uses Claude Code on a public repository — designed to prevent the AI from leaking internal information into commit messages and pull requests. Its instruction to Claude: “Do not blow your cover.”
It blocks references to internal model codenames, unreleased version numbers, internal Slack channels, and even the phrase “Claude Code” itself in public commits. There is no force-off switch — if not confident it is in an internal repo, it stays undercover. And the complete source of this subsystem was shipped in a .map file to npm — almost certainly built by the same toolchain it was designed to protect.
Animal Codenames & Internal Culture
The leak gives an unusually candid look at Anthropic’s internal naming. The project codename is Tengu — a Japanese mythological figure — appearing on hundreds of feature flags. Migration scripts revealed the Opus-era codename Fennec. Fast Mode’s API endpoint is unambiguously /claude_code_penguin_mode. Computer Use is internally called Chicago.
The Broader Pattern
This incident fits within a wider pattern of supply-chain risk in the JavaScript ecosystem — one examined in detail in the npm Axios supply chain attack analysis linked below. What makes the Claude Code case notable is who it happened to: a company whose primary product is AI safety, and whose CLI is itself responsible for writing and shipping code on behalf of users at scale.
Takeaways
For any developer publishing to npm: add *.map to your .npmignore, set sourcemap: false in production bundler config, and audit your published tarball with npm pack --dry-run before every release. Source maps are a debugging convenience — they should never ride to production registries.
The leaked codebase reveals genuinely sophisticated engineering. Anthropic is building significantly ahead of its public releases. Most of what was found — KAIROS, ULTRAPLAN, Buddy, coordinator swarms — is feature-gated and invisible in external builds. It just wasn’t invisible in the sourcemap.